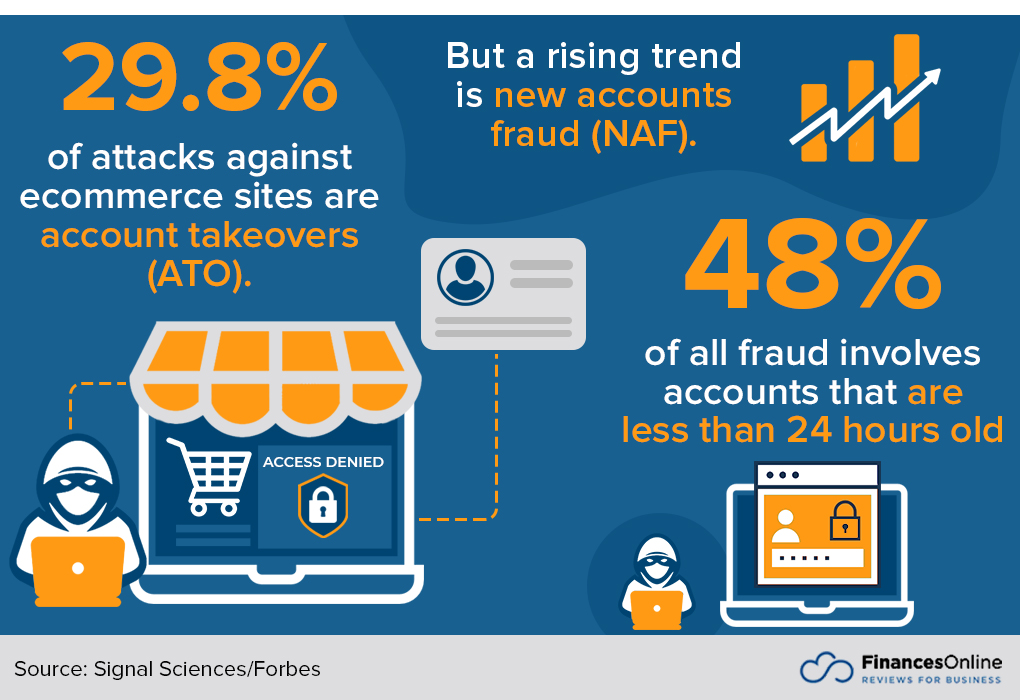
Per recent stats by exploding topics:
- eCommerce companies are estimated to lose $48 billion to fraud each year.
- Every $100 in fraudulent orders results in $207 in losses to the business.
- The average eCommerce company uses 5 fraud detection tools.
- 25% of eCommerce shoppers ask for a refund even though they plan on keeping the product.

From sign-ups to returns — every aspect of eCommerce operation is highly susceptible to fraudulent activities.
Imagine this: You’re a successful online retail business that has just launched an amazing Black Friday sale. The eyes of thousands of energetic shoppers light up as they rush to shop your website for the best deals in town.
However, alongside the rush of legitimate customers, there’s a handful of malicious ones who want to play the system to their advantage.
Not only do they place orders worth hundreds of dollars using stolen credit information but they also ‘dummy buy’ with signals confirming their intention to claim an unjustified refund.
Fraudulent activities can cause economic losses, but they also damage your brand reputation and customer loyalty, leading to a decrease in trust which can be difficult to regain.
So, where do you begin with neutralizing these threats? In this article, we will talk about what measures you can take to protect your ecommerce business.
Steps you can take to combat eCommerce fraud
Block sneaker bots
There’s a chance this term is new to you. Sneaker bots are automated software that shoppers use to cop or purchase, limited-edition goods usually touted as ‘products with instant resale value’ quicker than humanly possible.
Bots add items to their carts and check out faster than regular customers can even open the product page. They purchase items in bulk, usually for immediate resale at inflated prices. Blocking these bots prevents unfair practices and leaves the stock accessible to your legitimate customers.
Consider this — you’re a retailer selling limited-edition designer sneakers. Each release attracts regular shoppers, collectors, and fans, as well as bots intent on snatching all the stock. You want to ensure a fair purchase process for all, yet bots manage to inventory-hog in seconds, leaving your dedicated customers disappointed.
To block sneaker bots you need to combat gaming of the system. Protect legitimate customers by enabling CAPTCHAs, blocking repeat offenders’ IPs, or using bot management software.
Invest in a solid payment gateway
Merchants use payment gateways to accept payments from customers via debit or credit cards, both in-store (card-reading devices, payment terminals) and online (payment processing portals).
POS gateway providers offer a range of features including reporting, fraud detection, a smooth transaction experience, and tax calculations. They securely validate card details, guarantee available funds, and process the transaction.
Consider this: If an unethical customer inputs stolen credit card details during checkout, a robust payment gateway can detect anomalies in the transaction details. It may flag unusually high invoice sums compared to typical purchases or frequent transactions from the same IP address. Should such an activity arise, the transaction’s approval could get delayed or canceled to prevent economic loss.
Install SSL certificates
SSL (Secure Socket Layer) Certificates provide secure, encrypted communications between a website and an internet browser, thereby ensuring that all information passed between the two is private.
If your eCommerce platform is SSL-certified, it signifies trustworthiness to your customers. URLs that begin with “https” rather than “http” demonstrate that the site employs SSL. Most eCommerce platforms come with SSL as standard, but if yours doesn’t, you may need to purchase one separately.
Use 3D-Secure Checks
3D-Secure is a protocol designed to be an additional security layer for online credit and debit card transactions.
It adds an authentication step and has been widely adopted by Visa under the name ‘Verified by Visa’, by Mastercard as ‘Mastercard SecureCode’, and others.
Adding one extra level of verification, such as a dynamic one-time passcode sent to the consumer’s phone, can protect you from fraudulent purchases.
Incorporating 3D-Secure into the payment processing workflow can minimize fraudulent chargebacks, thereby reducing loss while retaining legitimate customers.
Implement a frictionless shopping experience
Shoppers appreciate a seamless, friction-free shopping experience. Inattention to customer convenience can lead to shopping cart abandonment.
However, balancing security measures and convenience may prove a tricky task for eCommerce sites. Overbearing security checks may deter genuine shoppers causing a decrease in sales.
This doesn’t have to be the case. Leveraging technology such as ‘risk-based authentication’ allows you to provide such a frictionless journey. It involves grading every purchase based on transaction risk factors such as the buyer’s purchasing habit.
Low-risk transactions go unnoticed, resulting in a smooth shopping experience, while the high-risk ones are flagged for additional review combating potential fraudulent activity.
Work with other retailers
Establish relationships with other retailers to exchange insights on potential fraud.
For example, you can share unique fraud trends or repeated problem IP addresses. With shared data, you can be proactive about recognizing fraud attempts in your system, detect suspicious buyer behavior, and strengthen fraud prevention strategies.
Regularly update system security
Credit card processors, eCommerce platforms, and IT infrastructure must be regularly updated to protect against recent threats.
Unscheduled security updates often patch vulnerabilities that hackers may have recently exploited.
Maintaining these updates prompts preventative action against malicious attacks, keeps website speed at optimum, and ensures customers have a hassle-free experience on your eCommerce platform.
Adopt machine learning
Machine learning algorithms can analyze patterns and identify fraudulent activities based on past behaviors, trends, and elements of predictability.
Machine learning considers variances in habit, breach attempts, and suspicious purchase trends, thereby providing a versatile, refined solution for battle scams.
Outsource cyber threat intelligence
Cyber threat intelligence providers can help to identify both current and emerging scams, threats, and vulnerabilities. They offer in-depth insights your in-house team might lose sight of or may not perceive instantly.
Including a third-party expert will add another line of defense and broaden your knowledge and analytical skills to face eCommerce insecurities.
Train your workforce effectively
Even with system mechanisms and outsourced help, your team forms the first line of defense against any form of violation.
Allocate annual, if not bi-annual, training for comprehensive understanding and recognizing of fraud patterns. Simultaneously, emphasize data privacy guidelines, confidentiality agreements, password protocols, and other relevant prescribed procedures.
Develop fraudulent behavior policies
Create tailored rules regarding detected e-commerce scams and the mandated steps to follow to remediate affected customers.
Clear guidelines assist employees during an actual fraudulent event.
For example: Let’s say there’s an incident where a multitude of transactions arises from the same IP address within a short period. Your procedure should have clear instructions on how to react, whether it means reaching out to the purported customer to verify the transactions or notifying your payment gateway to investigate the matter.
Purchase extensive fraud protection
Beyond SSL and 3D Secure Check, additional fraud protection proved as beneficial insurance against severe economic impact due to malicious activities.
Providers offer tracing cybercriminals, network breach notifications, reimbursement cover, and restoration of stolen data.
Utilize Multi-Factor Authentication (MFA)
Multi-factor authentication involves the use of two or more verification methods as a checkpoint before access is granted.
These methods typically categorize into something known by the user, something owned by the user, or something that is part of the user. This could be a passcode, a phone, or a fingerprint.
Its usage within eCommerce platforms can protect customer and transaction information, significantly deterring fraudulent activities.
Adapt Browser Fingerprinting
Browser fingerprinting can help you recognize a visiting device with a fair degree of certainty.
It taps data generated from a user’s unique browser settings, plugins, and operating system.
Not only does this enhance advertising efforts and customer eccentricity, but it also assists in identifying irregular or suspicious device activity and triggers necessary defense mechanisms against potential fraud.
Benefit from Geo-location and IP analysis
Geo-location tracking and IP analysis aid in positioning the whereabouts of users.
Identifying incongruous user locations is made possible through this tool which can hint at potential cyber threats or dispute claims. Conversely, scrutinized transactions from mutable IP pose less risk conversely uplifting customer’s shopping experiences.
Frequently Asked Questions
What is risk-based authentication?
Risk-based authentication is a security measure that ranks transactions according to a set list of risk factors, such as the buyer’s usual purchasing habits. Low-risk transactions typically bypass intense scrutiny, leading to a smooth customer journey.
How does machine learning aid in fraud detection?
Machine Learning allows your system to glean patterns and identify fraudulent activities based on historical data related to trends, behaviors, and predictable patterns.
What is Multi-Factor Authentication and its role in e-commerce platforms?
Multi-factor authentication (MFA) deploys two or more user checkpoint methods before providing access. Usually, these include components known by, owned by, or part of the user, for instance, a password, a device, or a biometric input like fingerprint or facial recognition.